Connect your Chromebook to your home network over SSH.
Dec 28This week i’m testing out my new Acer A730 to see just what it can do and how far we can take it. One of the frustrations I bumped in earlier this week was that there were limited options when it came to “Phoning home”. Setting up encrypted tunnels to your home network over the internet using VPN or Proxy connections is something we should consider when using public Wifi hotspots.
With the Chromebook relying completely on some wifi connection on a (perhaps foreign) network I was disappointed to find that the only protocols that were supported were L2TP and OpenVpn. Not a bad set to choose from but not something that I had setup on my home network.
Previously I used an SSH server and the SSHuttle app to tunnel my internet, dns and even network traffic over a Socks5 proxy to my home network. I wondered if this would be possible with the Chromebook. Turns out it is ! Let’s start cooking.
To get this little piece of magic working you need 3 things. A : One SSH server (A linux machine) on your home network that has at least one port open to the internet. B : The Secure Shell app from the Chrome store. C : The Switchy-Sharp extension.
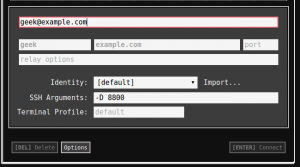
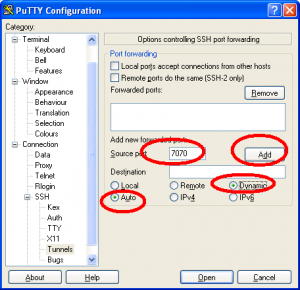
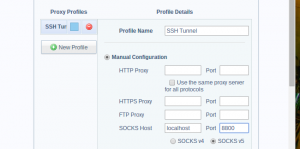
Setting it up is quite easy. Lets say we opened up port 8800 of our SSH server to the internet. Setup Secure Shell to connect to the your home SSH server with the additional option to create a port forwarding tunnel on lets say port 8800 with the option -D 8800
Next we setup Switchy Sharp as to use the SSH connection (and port 8800) as a socks 5 proxy.
All you need to do next is Connect to your home SSH server and use the Switchy Sharp extention in your browser to use the connection. The Chromebook will tunnel all http and https requests AND the DNS queries through the tunnel. That way 95% of your Chromebooks traffic (we aren”t a 100 percent sure about what protocols any other apps you have might use) are piped through a secure tunnel. You don’t only get to connect to your home network (to open up any web-interface to any device or server you have) but also you get to do it all ‘in private’
Links.
Related Posts
Chrome Week : Our favourite Chrome apps (Part 2)
Apr 14We already told you about some of our favourite Chrome apps in the first post of this series, So this time its time to dive a little deeper into applications/extensions that will actually help you to do things for which you otherwise would need an application. We have broken them down into some easy categories for you to follow.
Entertainment.
I think the days we actually stored music on our devices and played back those files are as obsolete as shouting “Put the needle on the Record” at some teen playing a DJ gig with his laptop. Since we are talking about Chrome extensions here, I can only assume that you have a connection to the internet all the time. With so many free audio streaming services available the only thing that is keeping you from playing the latest Shakira album over and over (and over) is your bandwidth cap. Some of the Chrome extensions we love here are Spotify and Soundcloud. Sure you get some commercials when you use the free service, but that’s just like real actual radio. If you should be in the business of running your own PLEX server at home and would like to stream your (audio and video) content on your Chromebook ? Try the Plex app. (But do make sure that you open up the right ports on your router if you want to access your server from the outside).
Production.
But what about when listening to music is not enough ? There are a couple of great apps out there that will actually help you MAKE some music. From simple voice recording with “Voice Recorder” to rather complex audio mixing with Audiotool. Want to annoy your friends by badly mixing 2 tracks together using an online DJ mixer ? Try Until AM.
Connecting to other machines.
But what if your Chromebook isn’t enough and you need to connect to other systems and devices ? When you need an SSH session to your Linux machine (or your mac) at home “Secure Shell” is without a shadow of a doubt one of our favourite applications. It reminds us of the popular Windows terminal client PUTTY only 4983 times better. It remembers sessions you have saved to your servers across multiple sessions of Chrome, so you always have your connections at your fingertips. If you need to go a step further and dive into the graphical side of things, you might want to try “Chrome RDP” to connect to your machines running the Remote Desktop Protocol.
Productivity.
Ok, The only reason you bought a Chromebook (or use Chrome) is so you can spend hours on 9gag and Reddit. So its a good thing we even dug up some productivity apps. Outlook.com might be a little bit of blasphemy in this Gmail centered environment, but the Chrome app DOES get you to your mailbox environment even though its not controlled by the “Big Bad G”. Another pretty simple Chrome app we found is called Workflow. Workflow lets you organise your tasks into lists and sub-lists. It’s more like a text based mindmap but it does give you a pretty good overview of what you are working on and what subtasks are involved. Speaking of “simple” and “text based” we found “Writer” to be a very nice distraction free text editor for writing up text without being distracted. We love the “black and green” terminal like interface, especially if you run the Chrome app fullscreen. Writer lets you download your writings to different formats or saves them to the cloud so you can continue editing them in another chrome browser.
And finally
With all the commotion about the Heartbleed exploit .. Install the Lastpass Chrome app and sort out your passwords once and for all.
Links.
- Spotify
- Soundcloud.
- Plex
- Voice Recorder
- Audiotool
- Until AM
- Secure Shell
- Chrome RDP
- Workflow
- Outlook.com
- Lastpass
- Writer
Related Posts
Server week : The essential SSH Server.
Mar 18This week in “Server week” we are going to set up a variety of servers that allow you to do a variety of things. One of the most basic and versatile server you can set up must be the SSH Server. Long time fans probably know that the SSH server is the base ingredient for a lot of fun stuff you can do. For example.
- Transfer files over the internet.
- Work with command line applications from a remote computer.
- Tunnel your browser traffic through your own server to stop nosy network admins.
- Connect to your home network with a VPN connection.
These are just a couple of things you can do, but before you can do that, you will need the basic ingredient : Let’s set up an SSH Server.
Required ingredients.
- Debian based Linux distribution : ( you can do it with a redhat based one too, but we use a debian based one for the tutorial)
- Static ip for your Linux distribution.
- Connection to the internet.
- If you don’t have a static IP : A dynamic DNS service like opendns or Dyndns.
- An open port on your router forwarded to your linux machine.
Let’s get cooking.
- Open up a terminal on your linux machine and type : sudo apt-get install openssh-server
- After the server is installed, connect to it from a remote machine using a terminal application like Putty (for Windows) Secure Shell (for the Chromebooks) or from the terminal on other Mac and Linux machines.
- Connect to your Linux server with the command : ssh yourusername@theipofyourserver
And starting out that is ALL you need to do. If you want to do this from the internet you need to forward the correct port (The standard port is Port 22) from your router to your linux machine so you can make it accessible from the internet.
Lets make it pretty.
- Want to have a unique login screen when you connect ? create a cool ASCII banner using THIS tutorial.
Lets make it secure.
- SSH servers run standard on port 22, so a lot of scriptkiddies will go around the internet and “knock” on your port 22 to see if there is a server there. We are going to “obscure” the location of your SSH server a little by changing the default portnumber (Remember you also need to adjust this on your server) Follow THIS tutorial to get you started.
- Next time you connect remember to connect with ssh -p portnumberyouchose yourusername@theipofyourserver
- If you want to get rid of entering your password when you connect you can log in using secure SSH keys. Its a little bit on the advanced geeky side but it DOES keep your machine extremely secure : Only a machine with a unique digital fingerprint can connect using this method : Here is a good tutorial.
Lets start using it.
The SSH server offers you a variety of functionalities we talked about in previous blogposts. We will line up the best uses for SSH here.
- Make a VPN connection to your home network using SSHUTTLE.
- Turn your server into a proxy server and tunnel all browser traffic though your home server. (here is the pdf howto)
- Keep an eye on what your server is doing.
- Run a remote supergeeky wordprocessor.
- Run remote graphical applications.
- Have a blast controlling your server from the command line.
- Run command line apps.
These are just a couple of examples of what you can do over this very powerful little SSH connection. Remember always to use strong passwords and keep your server up to date. Have fun !
Related Posts
Privacy Week : Tunnel traffic through your home network with Sshuttle.
Feb 06Today’s tip in our “Privacy week” is geared a little bit towards the more advanced geek .. (Who am I kidding, you are ALL advanced Geeks here). In our every lasting quest to ensure our privacy when surfing on “foreign networks” like the one at work, the one at your dorm or the free wifi hotspot at Starbucks , we try to find more ways to make sure all your web traffic is encrypted and your privacy is kept safe.
Enter SSHuttle ( NOOO , not the STAR TREK Shuttle) , A brilliant little transparent proxy application that directs ALL or PART of the network traffic from your trusty Linux or Mac machine (the laptop you use on the road) through an SSH tunnel to an SSH server of your choice (perhaps your own server at home). That way your traffic is completely (or partially) obscured from whoever is trying to sniff your traffic on an untrusted network. An added bonus is however that it is a transparent proxy ! This means your computer will actually think it is directly connected to the network where the SSH server is running. It is like running a very very very long cable through the internet straight from your machine to the network where your SSH server is located.
So let’s start cooking.
Ingredients.
- Laptop with a version of Debian Linux installed or a Mac running a recent version of OSX.
- An SSH server. ( Follow along our VERY OLD but still accurate manual on how to setup your own Linux SSH Server)
- A static IP address for your internet connection. (Or if you have a dynamic IP you can follow along with THIS great tutorial on how to use No-IP.org)
- Forwarding the correct port on your router. (Open up the port you are using for your SSH server from your router to the IP of the machine on which you are running the SSH Server)
How to install SSHuttle on your client machine.
- Install SSHuttle on your Linux machine using the command : sudo apt-get install sshuttle
- Install SSHuttle on your Mac by first installing HOMEBREW APP. (Installation instructions) and then typing brew install sshuttle
Shuttle is simple but VERY powerful. It will create an encrypted tunnel between your laptop and the SSH server you setup at home. Depending on what kind of traffic you want to shove through that tunnel you can do different things like :
- Just tunnel your browser traffic through the tunnel,
- Shove all of your web traffic through the tunnel (including dns requests),
- Shove ALL of your traffic through the tunnel.
- Set up a “site 2 site” VPN between the network you are working on and your network at home.
- … and more crazy stuff.
So how does it work ?
Once installed using SSHuttle is pretty simple. SSHuttle works from the command line and depending on the “switches” it will do different things for you. So on your client laptop , fire up your terminal and start typing.
-
sshuttle --dns -r username@yourremoteserver.com:2222 0/0
Enter the command above to push ALL of your traffic through the SSH tunnel towards your server at home. This is the example of running a virtual network cable THROUGH the internet towards your switch at home. All of your traffic is sent through this encrypted tunnel. USERNAME = A user you have created on your SSH server at home. YOURREMOTESERVER.COM = The external ip address (or Dynamic DNS name) of your home router. 2222 = The port on which you have your SSH server running. In this example I took a non-default port.
- sshuttle -r username@yourremoteserver.com:2222 192.168.0.0/24
With this command you can create a site to site VPN. Instead of typing 0/0 is going to send ALL the traffic through the tunnel. Typing the network range of your home network (in this case 192.168.0.0) tells SShuttle to send all the traffic that needs to go to the 192.168.0.0 domain through the tunnel, while sending out the rest of your traffic through whatever network gateway you are connected to. The /24 is your subnet mask ( you know , the 255.255.255.0 subnet number of your network).
There are a lot of other switches that you can use , but if you use the two commands we mentioned above you will have a LOT of power at your fingertips. I love using the second command. It allows me to connect to the exchange server at work for my work stuff, but also lets me quickly open up the web interface of my home router (on the LAN SIDE) to do some tinkering. SSHuttle is a very very nice tool that keeps you connected .. and keeps your privacy .. private.
Find out more about SSHUTTLE in this HAK5 episode.
Related Posts
Setting up your own SSH proxy on Windows.
Jan 22Free wifi is great. It’s like finding an oasis in the middle of the desert that gives you the ability to quench your digital thirst before you wade into the offline sahara once again. But “Open and Free” wifi comes at a price. Being a shared network medium, it means that all traffic on the wireless network is visible to all users on that network , should they care to take a peak.
With networking tools like “Wireshark” it is fairly easy sniff traffic on an open wifi network and intercept all kinds of unencrypted traffic. That traffic can consist of what URL’s you surf to to what passwords you use (if you have an unsecured connection) .. They are all there for anyone to sniff, download and analyse.
To keep your browser traffic private all you need to do is encrypt it. One of the ways to do this is of course use https connections where you can, but if that is not possible there are alternatives. You can set up your own SSH proxy server. This means you will be creating an encrypted tunnel from your laptop, TROUGH the internet, to your home server. Once there (behind the security of your own firewall) your traffic heads for the internet. Its like surfing at home, but you are in fact ‘away from home’.
The only thing you need are :
– Access over SSH to a linux server. ( Check our our tutorial on how to set this up)
– A copy of Firefox.
Setting it up is quite easy , and we will probably do a screencast on the issue in season 8 of our podcast, but instead of boring you with a lot of text , we are going to point you to the excellent podcast episode Kurtis Adkins did for Hacker Public Radio on the topic. Take 20 minutes and listen carefully. When you are done (and have the ingredients above) you will be able to secure your webtraffic from anyone who wants to snoop around. (Hackers, scriptkiddies or nosy sysadmins)
Link : Curtis Adkins on : Setting up and using SSH and SOCKS (Hacker public Radio ep 1422)